一、K8s多用户管理¶
1、创建一个专用于存储用户的Namespace
kubectl create ns kube-users
2、授权kube-users空间下的用户都有查看Namespace的权限
kubectl create clusterrolebinding namespace-readonly \
--clusterrole=namespace-readonly \
--group=system:serviceaccounts:kube-users
3、创建多个用户模拟不同的场景
# 创建用户project-a-develop
kubectl create sa project-a-develop -n kube-users
# 创建用户project-a-ops
kubectl create sa project-a-ops -n kube-users
4、创建Namespace模拟不同的环境
# 模拟开发环境
kubectl create ns project-a-dev
# 模拟测试环境
kubectl create ns project-a-test
# 模拟生产环境
kubectl create ns project-a-prod
5、在每个环境下创建一个服务
# 在project-a-dev下创建服务
kubectl create deploy redis --image=registry.cn-hangzhou.aliyuncs.com/abroad_images/redis:7.2.5 -n project-a-dev
# 在project-a-test下创建服务
kubectl create deploy redis --image=registry.cn-hangzhou.aliyuncs.com/abroad_images/redis:7.2.5 -n project-a-test
# 在project-a-prod下创建服务
kubectl create deploy redis --image=registry.cn-hangzhou.aliyuncs.com/abroad_images/redis:7.2.5 -n project-a-prod
二、不同用户授权管理¶
2.1 授权测试环境可以查看日志和执行命令¶
在非生产环境,可以针对开发和测试人员开放查看日志和执行命令的权限,方便排查问题等。
1、授权project-a-develop用户对project-a-dev这个空间可以有查看日志和执行命令的权限:
# 授权project-a-develop用户对project-a-dev有查看日志的权限
kubectl create rolebinding devop-pod-log \
--clusterrole=pod-log \
--serviceaccount=kube-users:project-a-develop -n project-a-dev
# 授权project-a-develop用户对project-a-dev有执行命令的权限
kubectl create rolebinding devop-pod-exec \
--clusterrole=pod-exec \
--serviceaccount=kube-users:project-a-develop -n project-a-dev
2、授权project-a-develop用户对project-a-test这个空间可以有查看日志和执行命令的权限:
# 授权project-a-develop用户对project-a-test有查看日志的权限
kubectl create rolebinding devop-pod-log \
--clusterrole=pod-log \
--serviceaccount=kube-users:project-a-develop -n project-a-test
# 授权project-a-develop用户对project-a-test有执行命令的权限
kubectl create rolebinding devop-pod-exec \
--clusterrole=pod-exec \
--serviceaccount=kube-users:project-a-develop -n project-a-test
3、创建Token测试
[root@k8s-master01 ~]# k create token project-a-develop -n kube-users
eyJhbGciOiJSUzI1NiIsImtpZCI6IjdxMWhLWkVpd0t3ZVpNNmdNNmhJdkdOaldfVzA0MTJySm84ZkpMbFhvLVkifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzQyOTYwNzIzLCJpYXQiOjE3NDI5NTcxMjMsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiNGYxM2UzODgtMzJkOS00YThiLTkyNjUtYWY5ZDRiNGNmMDgyIiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwic2VydmljZWFjY291bnQiOnsibmFtZSI6InByb2plY3QtYS1kZXZlbG9wIiwidWlkIjoiYmFhNjQ0ZmYtOWFhNC00MjVmLWJmMDUtOTA1OTk5MzgwYWQzIn19LCJuYmYiOjE3NDI5NTcxMjMsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXVzZXJzOnByb2plY3QtYS1kZXZlbG9wIn0.XMBpgv-AJFVp7D5TTHN84N5gIHABbfatDnwhMSdA1-czTcH3qO4emgGra_nUOC2ZgEZqWc6ApBkWnitGpWDkGIMYcdtgRInU30r3QKf8-UV1ydtFbO4ad-6hdansp1D7j85F0S_qC-7Y1MECpDnYdThoq8WBvuZxKJnZf53nxI4no0TNacxIkCKNPtETFQwpgmP5ZKn8MkoL72dcgG_ymXW9UBx9N_Xbr6El13ioJAeiIw3TPIeyRzvMhYIjRRMI9kV-kiyyBj3LZVR8vjBvxHz-F3QsTt3D2dczougcE5hSUEU74rTi7sFObZqRkk-zRz5fN2GtO3lFfW-GuU_y4Q
4、在浏览器中输入https://10.0.0.20:30401,复制上面token登录即可
[root@k8s-master01 ~]# kg svc -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.99.185.244 <none> 8000/TCP 12d
kubernetes-dashboard NodePort 10.109.201.212 <none> 443:30401/TCP 12d
5、命名空间选择project-a-dev,选择pods,观察到已有查看日志和执行命令的权限
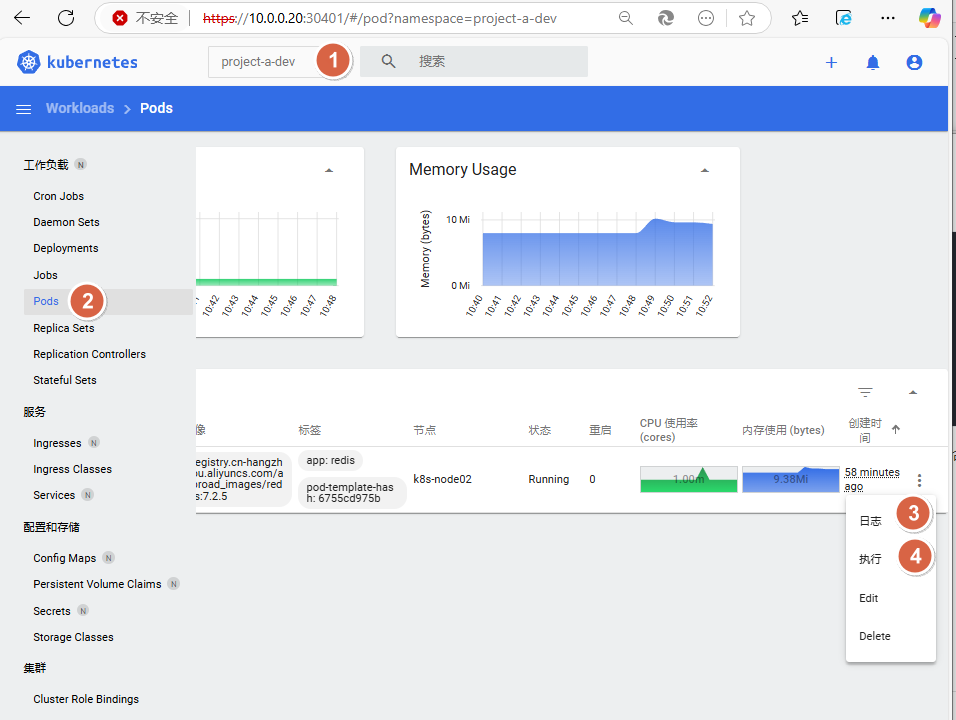
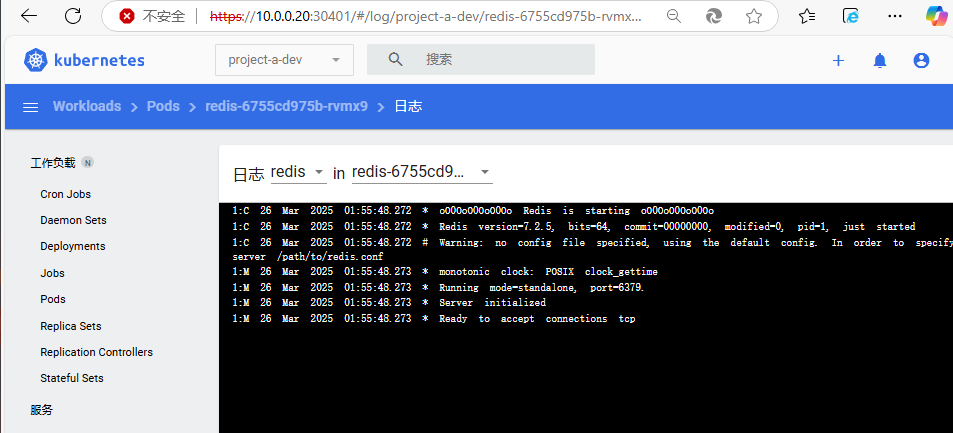
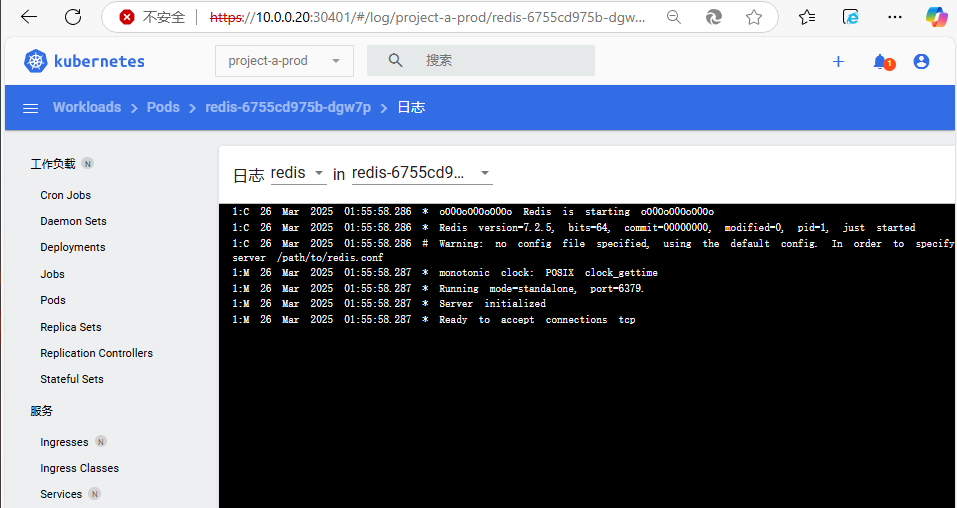
验证查看日志权限,观察到可以正常查看日志
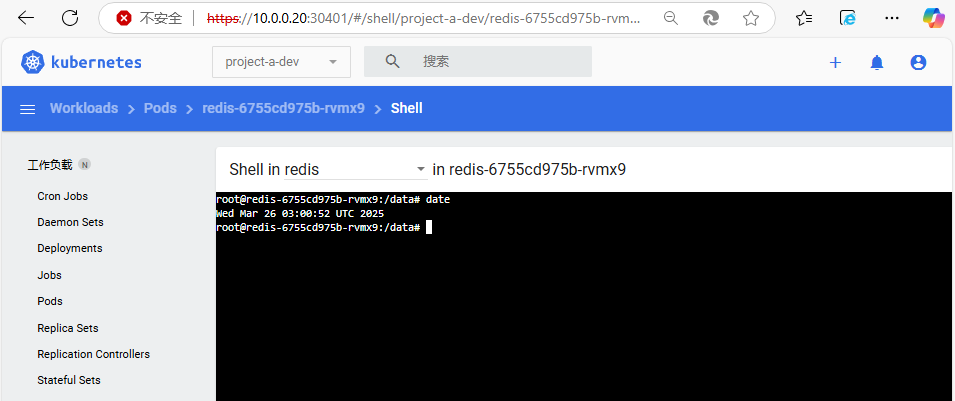
验证执行权限,观察到可以正常执行
2.2 授权生产环境只能查看日志¶
在生产环境,通常不允许其他用户有特别大的权限,此时可以限制只能查看日志。授权开发人员只能查看生产环境的日志权限:
1、授权project-a-develop用户对project-a-prod只有查看日志的权限
# 授权project-a-develop用户对project-a-prod有查看日志的权限
kubectl create rolebinding devop-pod-log \
--clusterrole=pod-log \
--serviceaccount=kube-users:project-a-develop -n project-a-prod
2、创建Token测试
[root@k8s-master01 ~]# k create token project-a-develop -n kube-users
eyJhbGciOiJSUzI1NiIsImtpZCI6IjdxMWhLWkVpd0t3ZVpNNmdNNmhJdkdOaldfVzA0MTJySm84ZkpMbFhvLVkifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzQyOTYwNzIzLCJpYXQiOjE3NDI5NTcxMjMsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiNGYxM2UzODgtMzJkOS00YThiLTkyNjUtYWY5ZDRiNGNmMDgyIiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwic2VydmljZWFjY291bnQiOnsibmFtZSI6InByb2plY3QtYS1kZXZlbG9wIiwidWlkIjoiYmFhNjQ0ZmYtOWFhNC00MjVmLWJmMDUtOTA1OTk5MzgwYWQzIn19LCJuYmYiOjE3NDI5NTcxMjMsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXVzZXJzOnByb2plY3QtYS1kZXZlbG9wIn0.XMBpgv-AJFVp7D5TTHN84N5gIHABbfatDnwhMSdA1-czTcH3qO4emgGra_nUOC2ZgEZqWc6ApBkWnitGpWDkGIMYcdtgRInU30r3QKf8-UV1ydtFbO4ad-6hdansp1D7j85F0S_qC-7Y1MECpDnYdThoq8WBvuZxKJnZf53nxI4no0TNacxIkCKNPtETFQwpgmP5ZKn8MkoL72dcgG_ymXW9UBx9N_Xbr6El13ioJAeiIw3TPIeyRzvMhYIjRRMI9kV-kiyyBj3LZVR8vjBvxHz-F3QsTt3D2dczougcE5hSUEU74rTi7sFObZqRkk-zRz5fN2GtO3lFfW-GuU_y4Q
3、在浏览器中输入https://10.0.0.20:30401,复制上面token登录即可
[root@k8s-master01 ~]# kg svc -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.99.185.244 <none> 8000/TCP 12d
kubernetes-dashboard NodePort 10.109.201.212 <none> 443:30401/TCP 12d
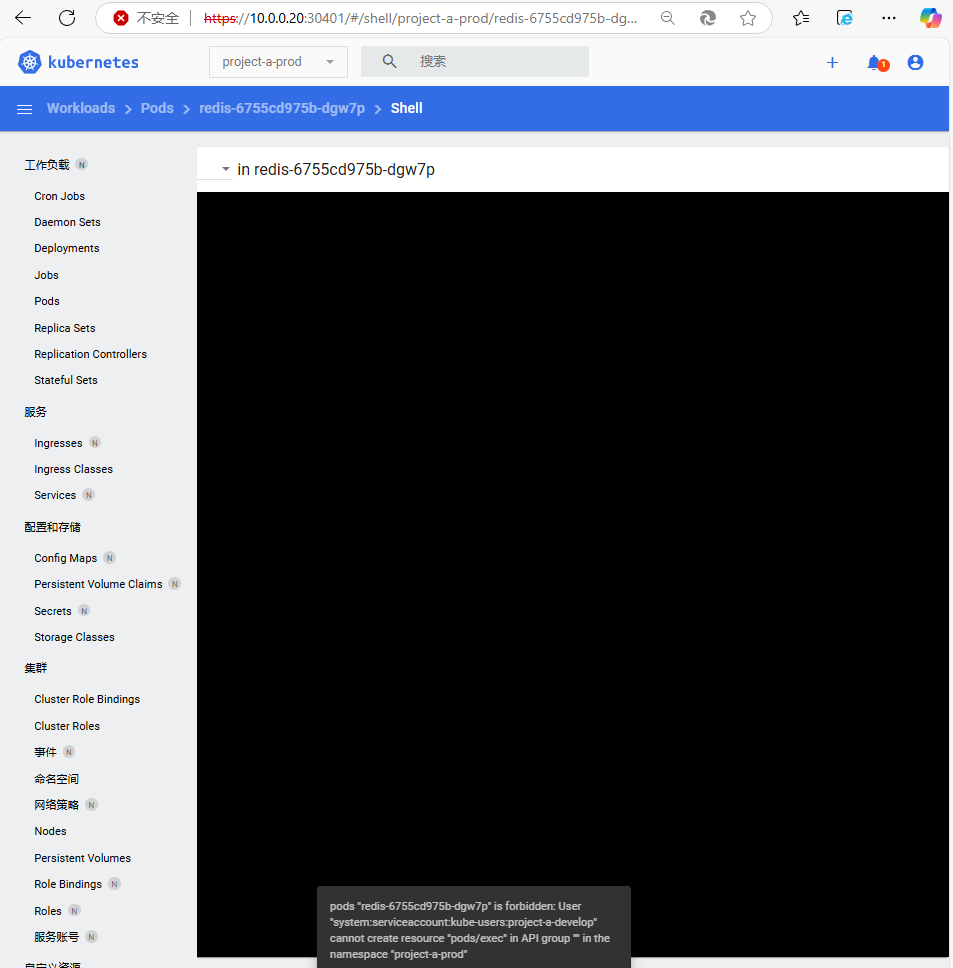
4、命名空间选择project-a-prod,选择pods,观察到只有查看日志的权限
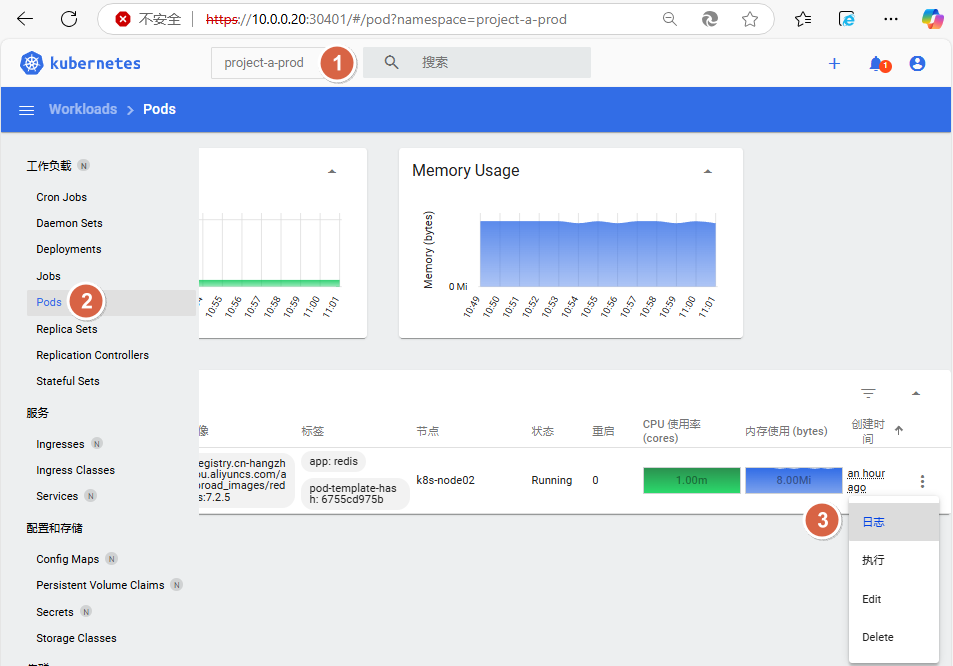
点击执行会因为没有权限产生报错信息