一、授权开发人员可以修改非生产环境部分资源¶
有时候开发人员需要修改程序的配置用来测试新功能或者排查故障,此时可以给开发人员授权可以编辑部分的资源,比如ConfigMap和Deployment
1、授权project-a-develop用户对project-a-dev有编辑ConfigMap和Deployment的权限
kubectl create rolebinding develop-configmap-deployment-manager \
--clusterrole=configmap-deployment-manager \
--serviceaccount=kube-users:project-a-develop -n project-a-dev
2、创建Token测试
[root@k8s-master01 ~]# k create token project-a-develop -n kube-users
eyJhbGciOiJSUzI1NiIsImtpZCI6IjdxMWhLWkVpd0t3ZVpNNmdNNmhJdkdOaldfVzA0MTJySm84ZkpMbFhvLVkifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzQyOTY1MDI1LCJpYXQiOjE3NDI5NjE0MjUsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiNzhjN2UxNWEtOWYyYi00ZDA1LTk4Y2QtOTQ1MTA4NzE3ZWI3Iiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwic2VydmljZWFjY291bnQiOnsibmFtZSI6InByb2plY3QtYS1kZXZlbG9wIiwidWlkIjoiYmFhNjQ0ZmYtOWFhNC00MjVmLWJmMDUtOTA1OTk5MzgwYWQzIn19LCJuYmYiOjE3NDI5NjE0MjUsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXVzZXJzOnByb2plY3QtYS1kZXZlbG9wIn0.mz26dJO7kXo31ZFK-jISMyY08K9inPAr-0Zx6DO9lUn7U1yoMh5JnHsZPTSku_kI6lPUEGAShvU5HA9Gn7ey7qbIjZuIWOKtaT-VFW8nNnzkKXYh1AiwIzPAO02t-cBy7rhA1st-Qb_8HL6h7fCXf6Adpbi0LLSJjpP51B7FGg2Hn9tPgvIK8SG8RU4s0GFdDvRAdhf8Ezv4jWDDSBrNgBO188U05pxaaViX9AZTR2ZoXO3kkfUYr-s2IiFg3jzSd17bvtZjNJi1Sin92QZI0b9fJj3ZM-s89DmYiqLyIJv771otbX5EpTyUnpsYDnEXzHxXQdi46ttmWXyos9nRIw
3、在浏览器中输入https://10.0.0.20:30401,复制上面token登录即可
[root@k8s-master01 ~]# kg svc -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.99.185.244 <none> 8000/TCP 12d
kubernetes-dashboard NodePort 10.109.201.212 <none> 443:30401/TCP 12d
4、命名空间选择project-a-dev,选择Deployments,点击重启
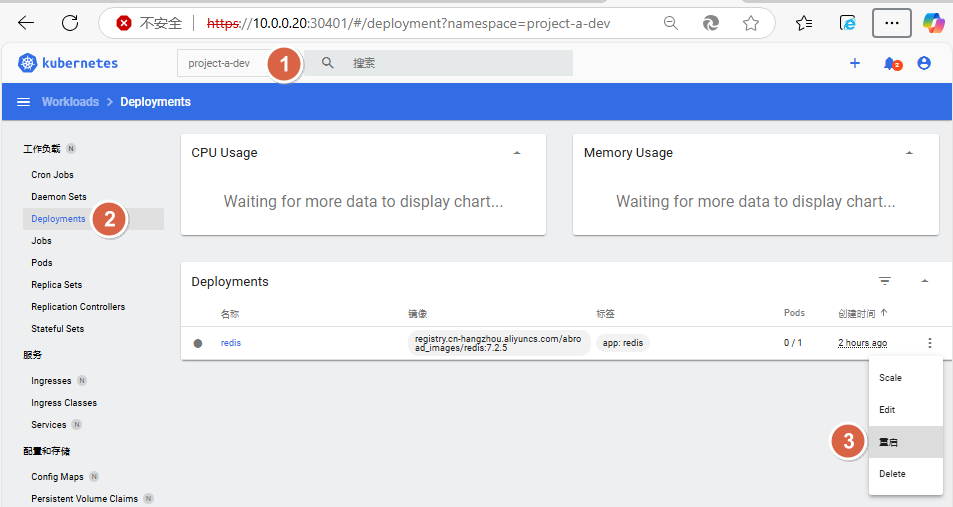
因前台数据有延迟,后台验证deploy重启成功
[root@k8s-master01 ~]# kgp -n project-a-dev
NAME READY STATUS RESTARTS AGE
redis-5f9c77fdf8-drtkv 1/1 Running 0 27s
二、授权多租户场景受限管理员的权限¶
如果集群中分配了多个租户和OPS用户,此时租户和OPS用户应当具备指定空间的所有权限,此时可以直接使用admin或者edit的ClusterRole进行授权:
比如授权project--a-ops用户可以操作project-a-dev、project-a-test、project-a-prod空间下的所有资源:
1、授权project--a-ops用户可以操作project-a-dev、project-a-test、project-a-prod空间下的所有资源
# 授权project--a-ops用户可以操作project-a-dev空间下的所有资源
kubectl create rolebinding ops-edit \
--clusterrole=edit \
--serviceaccount=kube-users:project-a-ops -n project-a-dev
# 授权project--a-ops用户可以操作project-a-test空间下的所有资源
kubectl create rolebinding ops-edit \
--clusterrole=edit \
--serviceaccount=kube-users:project-a-ops -n project-a-test
# 授权project--a-ops用户可以操作project-a-prod空间下的所有资源
kubectl create rolebinding ops-edit \
--clusterrole=edit \
--serviceaccount=kube-users:project-a-ops -n project-a-prod
2、创建Token测试
[root@k8s-master01 ~]# k create token project-a-develop -n kube-users
eyJhbGciOiJSUzI1NiIsImtpZCI6IjdxMWhLWkVpd0t3ZVpNNmdNNmhJdkdOaldfVzA0MTJySm84ZkpMbFhvLVkifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzQyOTY1MDI1LCJpYXQiOjE3NDI5NjE0MjUsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiNzhjN2UxNWEtOWYyYi00ZDA1LTk4Y2QtOTQ1MTA4NzE3ZWI3Iiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwic2VydmljZWFjY291bnQiOnsibmFtZSI6InByb2plY3QtYS1kZXZlbG9wIiwidWlkIjoiYmFhNjQ0ZmYtOWFhNC00MjVmLWJmMDUtOTA1OTk5MzgwYWQzIn19LCJuYmYiOjE3NDI5NjE0MjUsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXVzZXJzOnByb2plY3QtYS1kZXZlbG9wIn0.mz26dJO7kXo31ZFK-jISMyY08K9inPAr-0Zx6DO9lUn7U1yoMh5JnHsZPTSku_kI6lPUEGAShvU5HA9Gn7ey7qbIjZuIWOKtaT-VFW8nNnzkKXYh1AiwIzPAO02t-cBy7rhA1st-Qb_8HL6h7fCXf6Adpbi0LLSJjpP51B7FGg2Hn9tPgvIK8SG8RU4s0GFdDvRAdhf8Ezv4jWDDSBrNgBO188U05pxaaViX9AZTR2ZoXO3kkfUYr-s2IiFg3jzSd17bvtZjNJi1Sin92QZI0b9fJj3ZM-s89DmYiqLyIJv771otbX5EpTyUnpsYDnEXzHxXQdi46ttmWXyos9nRIw
3、在浏览器中输入https://10.0.0.20:30401,复制上面token登录即可
[root@k8s-master01 ~]# kg svc -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.99.185.244 <none> 8000/TCP 12d
kubernetes-dashboard NodePort 10.109.201.212 <none> 443:30401/TCP 12d
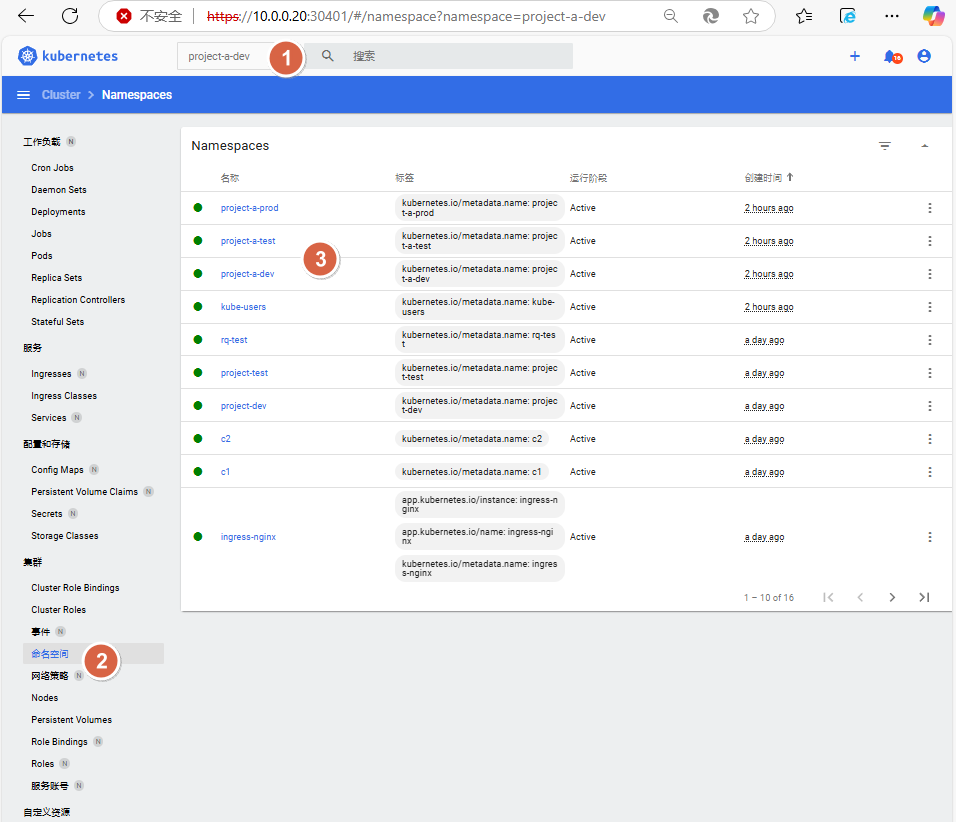
4、命名空间分别选择project-a-dev、project-a-test、project-a-prod,观察到此时可操作上述空间的大部分资源
三、授权应用程序可以访问集群资源¶
有时候需要对部署在Kubernetes集群中的服务进行授权,使其可以访问资源的某些资源,比如获取集群中的Pod状态等,此时可以授权给某个ServiceAccount,然后让Pod用该ServiceAccount创建Pod,此时该Pod内的程序即可具备相关的权限。
比如要实现某个程序具备view的权限,可以用如下方式进行授权。
1、创建一个用于该程序的ServiceAccount
kubectl create sa app-view -n project-a-dev
2、授权该ServiceAccount
kubectl create rolebinding app-view \
--clusterrole=view \
--serviceaccount=project-a-dev:app-view -n project-a-dev
3、创建一个资源,并使用该ServiceAccount
# 创建资源
kubectl create deploy app --image=registry.cn-hangzhou.aliyuncs.com/abroad_images/kubectl -n project-a-dev -- sleep 3600
# 验证
[root@k8s-master01 ~]# kgp -n project-a-dev | grep app
app-59ddf87bb5-n5jm6 1/1 Running 0 4m30s
# 获取当前资源的ServiceAccount值
[root@k8s-master01 ~]# kgp -n project-a-dev app-59ddf87bb5-n5jm6 -oyaml | grep -i ServiceAccount
- mountPath: /var/run/secrets/kubernetes.io/serviceaccount
serviceAccount: default
serviceAccountName: default
- serviceAccountToken:
- mountPath: /var/run/secrets/kubernetes.io/serviceaccount
4、修改ServiceAccount为app-view
[root@k8s-master01 ~]# kubectl edit deploy app -n project-a-dev
# 第35行内容下面添加serviceAccountName: app-view
...
...
serviceAccountName: app-view
...
...
验证是否修改成功
# 验证查看
[root@k8s-master01 ~]# kgp -n project-a-dev | grep app
app-5d798fdb45-zg665 1/1 Running 0 2m2s
# 观察到已经成功修改
[root@k8s-master01 ~]# kgp -n project-a-dev app-5d798fdb45-zg665 -oyaml | grep -i ServiceAccount
- mountPath: /var/run/secrets/kubernetes.io/serviceaccount
serviceAccount: app-view
serviceAccountName: app-view
- serviceAccountToken:
- mountPath: /var/run/secrets/kubernetes.io/serviceaccount
5、进入容器中进行测试,观察到程序应用可以对project-a-dev命名空间下的资源进行操作
[root@k8s-master01 ~]# k exec -it app-5d798fdb45-zg665 -n project-a-dev -- bash
# 这里注意进去后默认命名空间为project-a-dev
I have no name!@app-5d798fdb45-zg665:/$ kubectl get po
NAME READY STATUS RESTARTS AGE
app-5d798fdb45-zg665 1/1 Running 0 5m12s
redis-5f9c77fdf8-drtkv 1/1 Running 0 50m
其他空间未授权访问
I have no name!@app-5d798fdb45-zg665:/$ kubectl get po -n project-a-test
Error from server (Forbidden): pods is forbidden: User "system:serviceaccount:project-a-dev:app-view" cannot list resource "pods" in API group "" in the namespace "project-a-test"
如果需要访问project-a-test空间的资源,按需创建RoleBinding即可
# 创建测试命名空间(如果已经创建可忽略)
kubectl create ns project-a-test
# 创建跨命名空间 RoleBinding
kubectl create rolebinding app-view-cross-test \
--clusterrole=view \
--serviceaccount=project-a-dev:app-view \
-n project-a-test
# 验证权限
I have no name!@app-5d798fdb45-zg665:/$ kubectl get po -n project-a-test
NAME READY STATUS RESTARTS AGE
redis-6755cd975b-cxthw 1/1 Running 0 3h6m
